You might have heard that Blockchain is immutable, but that is a lie!... well not quite, but the ledger is technically modifiable.
One of the many things I found very interesting about the concept of Blockchain introduced by Bitcoin, is how the Proof of Work model works, and how it makes the blockchain immutable (among other things). Specially when you consider that digital data can always be modified, no matter what. The blockchain technology deals with it, and thinks ahead. That’s an important aspect when you are trying to build a system for transferring value in a trustless* way.
The Proof of Work
(if you already know what “Proof of Work” is, you can skip to the next section)
Let’s say we have a ledger to keep records of many transactions, and let’s say we want that ledger to be distributed among all the participants of the network (i.e., copied on everyone’s computers). If you are thinking of Bitcoin, you are on the right path.
The thing with a distributed ledger is that the goal is for everyone to have a copy and verify it… but also to allow everyone/all to maintain it. That’s the tricky part because “how, when and who is allowed to add records to that ledger?”. You will need some kind of consensus to do that, and that is when Proof of Work (PoW) enters the scene.
To put it simply, Proof of Work means that there is evidence that certain participant of the network really did perform a specific task (work) and invested resources in order to do so, hence the name Proof of Work. Using certain computational techniques, that evidence can be provided.
So why is it important to demonstrate that someone invested time and energy (resources) in performing certain task?
The consensus rules of the blockchain (as established by the Bitcoin protocol) dictates that, in order to add new records to the ledger, a participant has to perform some specific tasks and then provide proof that he invested resources by performing computational calculations. The first participant to do all that successfully will be allowed to add those new records to the distributed/shared ledger, and the rest of the network will accept that as part of the global database. That is part of what’s called “mining” by the way.
This previously (and briefly) described process, plus some economics, is what makes the consensus work and prevents (or vastly reduces) the possibility of counterfeits or attacks on that ledger.
The inevitable change
In the digital world, the idea of something not being able to be changed just makes no sense. Anything that is in a digital form can be altered and copied. And not only the digital world allows things to be changed and duplicated, but also does it with an extremely lower cost compared to other forms of content storage. Think of editing a document vs changing your writing in a piece of paper or changing the engraving of a stone; or think of copying a digital image file vs replicating a painting. And if you scale that, the difference is even bigger. This feature of the digital content, besides being an obvious benefit in many cases, represents a problem in some specific scenarios when you want to avoid other parties from copying or changing some content digitally stored, either for data integrity, copyrights, or any other reason.
Let’s say I downloaded a text (.txt) file created by someone else. Nobody can prevent me from opening that file with my favorite text editor, change whatever I want on it and save it. Now I have an altered version of that original file, and it costs me almost nothing. The same goes if I download an image, change it with my favorite image editor, and save it.
Validity and Utility
The question is, however, if the altered content I have now is valid and useful for me.
What do I mean by “valid” and “useful”? Well, let me try a vague definition. I assume something is valid if it still is what it means to be (a text file, an image or a song). And I assume something is useful if it performs the task it is expected to perform, with the expected result. Both concepts are actually very intertwined.
So, for the examples I mentioned before, we can all agree that they are still valid and useful for me after the modification. But what if I want to modify the executable of a software I like to make it behave differently? Well I could open it again with my favorite text editor, replace a few weird characters (if you are not a tech person, I dare you to open an executable file with a text editor to see what I mean), save it and try to execute it. The software won’t probably run and I now have an altered version that was very easy and cheap to modify, but is neither valid or useful for me.
There are of course people with sufficient knowledge that can alter those executable files properly to make them work as expected. So in that example, the only thing different from before was an additional obstacle to reach the “validity” and “utility” desired, but not the ability to alter the file itself, which we can say it’s intrinsic to digital content.
In any case, nobody can prevent me from making modifications on digital content I have access to. What they can do is making that technically harder for me to do, or find a way to dissuade me if I make altered copies of that digital material. You can easily think of real world examples for the second scenario with laws and punishments regarding piracy or copyright infraction... And you can also see how that worked out so far.
The network approval
The interesting path to discuss here is about making it harder for the altered versions to be valid and useful, arguably more effective than reactive actions like laws or punishments. Over time this has been (and still is) tried many times, and many times it was unsuccessful. No matter how many activation keys, authoring signatures or whatever piece of data the content supposedly required to be used, someone could always find a way to forge that piece of data, or even bypass the very validation itself in the first place and use the content anyways. Because the logic is, why does it matter as long as “this” keeps being useful for “that” (this audio file for listening, this document for reading, this software for running).
However, the picture changes when the validity and (even more) the utility of that content depends on the approval of a network. For example, that would be the case if my software needs to be connected to a certain network to run, or if my newly altered content is only useful if it’s accepted by the rest of the network. In this new scenario, it’s no longer enough for the digital content to be valid in front of my eyes, it also needs to be valid in the eyes of the rest of the network. And that is something much more harder to achieve by ourselves.
Software and gaming industry have been moving towards this path by including accounts and registration to allow users use their products, and also and more importantly, adding real value to those products if you are granted that membership. So, if I wanted to alter my digital product I might be able to use it for a limited set of purposes, but if I want to access those novel features provided by the network (p2p online gaming, periodic upgrades, to name a few) my altered software won’t be able to pass that validation.
But how that works? That works because there is a central authority that oversees each digital content exchange, and makes sure everything is according to the rules they defined. And everything that is not, is not allowed to participate. In this case, the company that created that software is usually that central authority. But this model can also be bypassed by creating parallel networks where our altered product is valid and useful, and we’ve seen that as well.
The decentralized network approval
But what happens if we have a content that is stored in a distributed way, and we want the entire system to be distributed without any central authority? We are talking about something like the Bitcoin ledger, of course, and that is when Proof of Works enters the scene again.
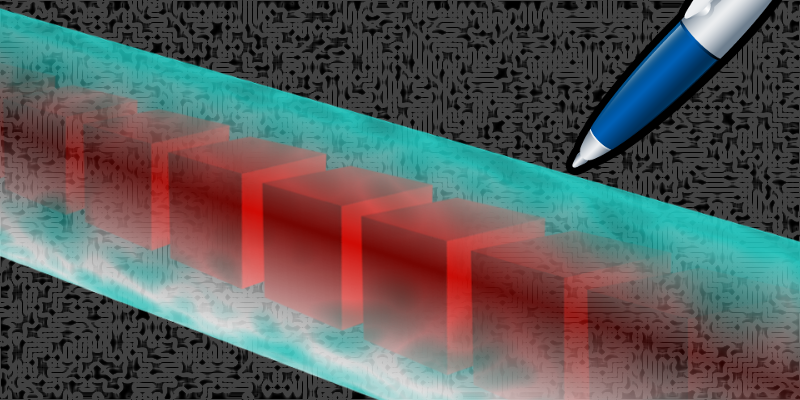
Technically speaking PoW doesn’t make it harder to alter the data in the ledger; doing only that is extremely easy. What PoW does is making it extremely difficult for that new modified data to be accepted by the community (validity) and eventually make such modification worth it (utility). That is because PoW establishes that the chain of blocks with the most accumulated work is the valid one. Which means that if I want to change the past in the ledger, I will need to do at least as much work (i.e., provide proof of work) as the amount done from that point in the past until the present. And that is without considering that while I’m doing all of that, the “present” point keeps moving forward as more blocks are being generated.
One key aspect here in a decentralized scenario, is that I would need my new modified content to be accepted by that network, and by all of it, in order to be valid and useful. Otherwise I will end up in a parallel network, and that won’t serve my purpose.
In practical terms, with Bitcoin (or other value transfer crypto on blockchain with PoW) as an example, even if I could remove a transaction from the ledger to perform a double-spend, I wouldn’t be able to get that change accepted through the network fast enough for it to become the new truth and allow me to spend those coins again.
So, to sum up, the whole idea behind immutability is that in order to make a change be worth it (valid and useful), the amount of work required is so huge that it becomes not worth it. That is a clever way of keeping things working as expected.
Final thoughts
The previous line of reasoning didn’t result in a fantastic revelation, and I don’t expect you to think that this article is. But that was instead a realization on the conceptual approach to immutability in digital content: start with the premise that digital content will always be susceptible of modification, and work on the validity and utility of that content in a network context.
I now wonder is the same approach can be applied to other aspects of our society and the human experience, specially if they are immerse into a network. Perhaps there are some actions people do that society wants to prevent; and instead of devising rules that people may or may not follow, or instead of thinking of different punishments to dissuade people from committing those actions, we can think of a way of making those actions irrelevant and lacking of value in the network. In other words, making the effort of getting value from those actions so high, that people will think it’s not worth it. That way there will be no incentive in pursuing that course of action.
Bitcoin kind of did that for “stealing money” by also making money a decentralized construct (fully dependent on network acceptance).
I don’t have any specific insight on some practical scenario yet, so I’ll keep the concept of Proof of Work for future inspiration.
Feel free to comment and give me your feedback. All suggestions are welcome!

